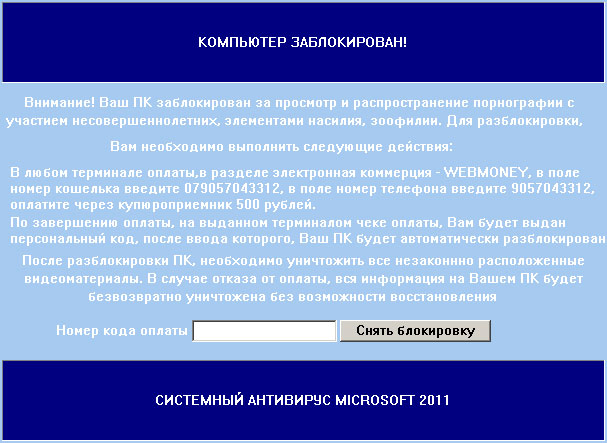
КОМПЬЮТЕР ЗАБЛОКИРОВАН!
Внимание! Ваш ПК заблокирован за просмотр и распространение порнографии с
участием несовершеннолетних, элементами насилия, зоофилии. Для разблокировки,
Вам необходимо выполнить следующие действия:
В любом терминале оплаты,в разделе электронная коммерция - WEBMONEY, в поле
номер кошелька введите [], в поле номер телефона введите [],
оплатите через купюроприемник 500 рублей.
По завершению оплаты, на выданном терминалом чеке оплаты, Вам будет выдан
персональный код, после ввода которого, Ваш ПК будет автоматически разблокирован.
После разблокировки ПК, необходимо уничтожить все незаконнно расположенные
видеоматериалы. В случае отказа от оплаты, вся информация на Вашем ПК будет
безвозвратно уничтожена без возможности восстановления
СИСТЕМНЫЙ АНТИВИРУС MICROSOFT 2011
СИСТЕМНЫЙ АНТИВИРУС MICROSOFT 2011 malware removal instructions:
1. Reboot your computer is "Safe Mode with Command Prompt". As the computer is booting tap the "F8 key" continuously which should bring up the "Windows Advanced Options Menu" as shown below. Use your arrow keys to move to "Safe Mode with Command Prompt" and press Enter key. Login as the same user you were previously logged in with in the normal Windows mode. Read more detailed instructions here: http://www.computerhope.com/issues/chsafe.htm

2. When Windows loads, the Windows command prompt will show up as show in the image below. At the command prompt, type explorer, and press Enter. Windows Explorer opens. Do not close it.

3. Then open the Registry editor using the same Windows command prompt. Type regedit and press Enter. The Registry Editor opens.

4. Locate the following registry entries:
HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\
In the righthand pane select the registry key named Shell. Right click on this registry key and choose Delete.

HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\
In the righthand pane select the registry key named Shell. Right click on this registry key and choose Modify.

Default value is Explorer.exe.

Modified value data points to Trojan Ransomware executable file.

Please copy the location of the executable file it points to into Notepad or otherwise note it and then change value data to Explorer.exe. Click OK to save your changes and exit the Registry editor.
5. Remove the malicous file. Use the file location you saved into Notepad or otherwise noted in step in previous step. In our case, "СИСТЕМНЫЙ АНТИВИРУС MICROSOFT 2011" was run from the My Documents. There was a file called porn_video.exe.
Full path: C:\Documents and Settings\Michael\My Documents\porn_video.exe

Go back into "Normal Mode". To restart your computer, at the command prompt, type shutdown /r /t 0 and press Enter.

6. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe, explorer.exe or winlogon.exe. With all of these tools, if running Windows 7 or Vista they MUST be run as Auto Infoistrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
7. If the problem persists, please follow the general Trojan.Ransomware removal guide.
Associated СИСТЕМНЫЙ АНТИВИРУС MICROSOFT 2011 ransomware files and registry values:
Files:
- [SET OF RANDOM CHARACTERS].exe
- HKEY_LOCAL_MACHINE\SOFTWARE\Microsoft\Windows NT\CurrentVersion\Winlogon\ "Shell" = "[SET OF RANDOM CHARACTERS].exe"
- HKEY_CURRENT_USER\Software\Microsoft\Windows NT\CurrentVersion\Winlogon\ Shell" = "[SET OF RANDOM CHARACTERS].exe"
No comments:
Post a Comment