
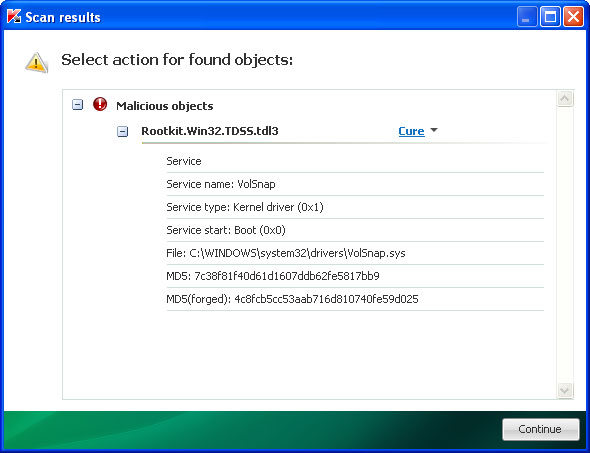
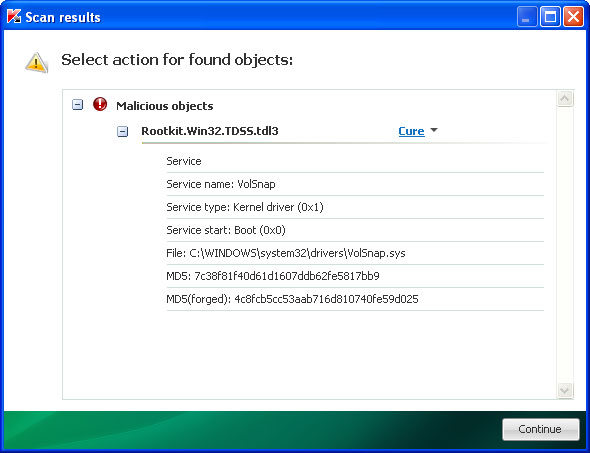
There are numerous things to keep in mind when removing HDD Repair. First, of all, do not delete any files from Temp folder either manually or using such system cleaners as CCleaner. The rogue programs moves software shortcuts from various locations to %Temp%\smtmp folder. If you delete the smtmp folder, you will lose your software and system shortcuts. Secondly, HDD Repair may turn your Dekstop background black and hide the rest of files. Thirdly, this rogue program may drop a rootkit, very often TDL4 from the TDSS family. It may drop other type of malware too. You can use TDSSKiller to check whether your computer is infected with a rootkit or not.
Fake HDD Repair warnings:

Additionally, you can activate the rogue program by entering this registration code 8475082234984902023718742058948 and any email as shown in the image below.

Once this is done, you are free to install anti-malware software and remove the rogue anti-virus program from your computer properly. And remember, do not purchase HDD Repair. If you have already bought it, please contact your credit card company and dispute the charges. If you have any questions or need additional help removing HDD Repair, please leave a comment below or email us. Compute wisely!
HDD Repair removal instructions:
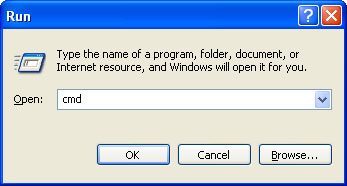
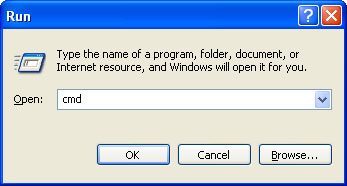
1. First of all, you need to unhide the files and folders. Select Run... from the Start Menu or just hit the key combination CTRL+R on your keyboard. In the Open: field, enter cmd and hit Enter or click OK.
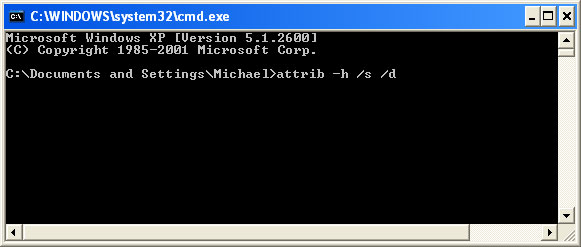
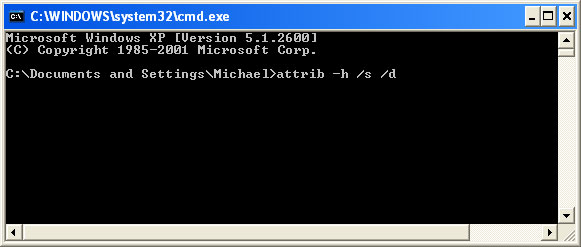
At the command prompt, enter attrib -h /s /d and hit Enter. Now, you should see all your files and folders. NOTE: you may have to repeat this step because the malware may hide your files again.
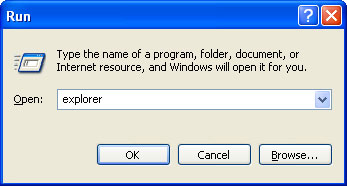
If you still can't see any of your files, Select Run... from the Start Menu or just hit the key combination CTRL+R on your keyboard. In the Open: field, enter explorer and hit Enter or click OK.
2. Open Internet Explorer. Select Run... from the Start Menu or just hit the key combination CTRL+R on your keyboard. In the Open: field, enter iexplore.exe and hit Enter or click OK.
Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as Auto Infoistrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
3. Open Internet Explorer and download TDSSKiller or Backdoor.Tidserv Removal Tool. This malware usually (but not always) comes bundled with TDSS rootkit. Removing this rootkit from your computer is very important (if exists). Run TDSSKiller or Backdoor.Tidserv Removal Tool to remove the rootkit.
Alertane HDD Repair removal instructions:
1. First of all, you need to unhide the files and folders. Select Run... from the Start Menu or just hit the key combination CTRL+R on your keyboard. In the Open: field, enter cmd and hit Enter or click OK.
At the command prompt, enter attrib -h /s /d and hit Enter. Now, you should see all your files and folders. NOTE: you may have to repeat this step because the malware may hide your files again.
2. The rogue application places an icon or your desktop. Right click on the icon, click Properties in the drop-down menu, then click the Shortcut tab.

The location of the malware is in the Target box.

On computers running Windows XP, malware hides in:
C:\Documents and Settings\All Users\Application Data\
NOTE: by default, Application Data folder is hidden. Malware files are hidden as well. To see hidden files and folders, please read Show Hidden Files and Folders in Windows.
Under the Hidden files and folders section, click Show hidden files and folders, and remove the checkmark from the checkbox labeled:
- Hide extensions for known file types
- Hide protected operating system files
Click OK to save the changes. Now you will be able to see all files and folders in the Application Data directory.
On computers running Windows Vista/7, malware hides in:
C:\ProgramData\
3. Look for suspect ".exe" files in the given directories depending on the Windows version you have.
Example Windows XP:
C:\Documents and Settings\All Users\Application Data\16441124.exe
C:\Documents and Settings\All Users\Application Data\fWpYMRQgdRYv.exe
Example Windows Vista/7:
C:\ProgramData\16441124.exe
C:\ProgramData\fWpYMRQgdRYv.exe
Basically, there will be a couple of ".exe" file named with a series of numbers or letters.

Rename those files to 16441124.vir, fWpYMRQgdRYv.vir etc. For example:

It should be: C:\Documents and Settings\All Users\Application Data\16441124.vir
Instead of: C:\Documents and Settings\All Users\Application Data\16441124.exe
4. Restart your computer. The malware should be inactive after the restart.
5. Open Internet Explorer and download TDSSKiller or Backdoor.Tidserv Removal Tool. This malware usually (but not always) comes bundled with TDSS rootkit. Removing this rootkit from your computer is very important (if exists). Run TDSSKiller and remove the rootkit.
6. Download free anti-malware software from the list below and run a full system scan.
NOTE: in some cases the rogue program may block anti-malware software. Before saving the selected program onto your computer, you may have to rename the installer to iexplore.exe or winlogon.exe With all of these tools, if running Windows 7 or Vista they MUST be run as Auto Infoistrator. Launch the program and follow the prompts. Don't forget to update the installed program before scanning.
7. New threats appear every day. In order to protect your PC from such (new) infections we strongly recommend you to use ESET Smart Security.
Associated HDD Repair files and registry values:
Files:
Windows XP:
- %AllUsersProfile%\Application Data\[SET OF RANDOM CHARACTERS]
- %AllUsersProfile%\Application Data\[SET OF RANDOM CHARACTERS].exe
- %UsersProfile%\Desktop\HDD Repair.lnk
- %UsersProfile%\Start Menu\Programs\HDD Repair
- %UsersProfile%\Start Menu\Programs\HDD Repair\HDD Repair.lnk
- %UsersProfile%\Start Menu\Programs\HDD Repair\Uninstall HDD Repair.lnk
%UserProfile% refers to: C:\Documents and Settings\[User Name]
Windows Vista/7:
- %AllUsersProfile%\[SET OF RANDOM CHARACTERS]
- %AllUsersProfile%\[SET OF RANDOM CHARACTERS].exe
- %UsersProfile%\Desktop\HDD Repair.lnk
- %UsersProfile%\Start Menu\Programs\HDD Repair\
- %UsersProfile%\Start Menu\Programs\HDD Repair\HDD Repair.lnk
- %UsersProfile%\Start Menu\Programs\HDD Repair\Uninstall HDD Repair.lnk
%UserProfile% refers to: C:\Users\[User Name]
Registry values:
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS].exe"
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Run "[SET OF RANDOM CHARACTERS]"
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Associations "LowRiskFileTypes" = '/{hq:/s`s:/ogn:/uyu:/dyd:/c`u:/bnl:/ble:/sdf:/lrh:/iul:/iulm:/fhg:/clq:/kqf:/`wh:/lqf:/lqdf:/lnw:/lq2:/l2t:/v`w:/rbs:'
- HKEY_CURRENT_USER\Software\Microsoft\Windows\CurrentVersion\Policies\Attachments "SaveZoneInformation" = '1'
- HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Download "CheckExeSignatures" = 'no'
- HKEY_CURRENT_USER\Software\Microsoft\Internet Explorer\Main "Use FormSuggest" = 'yes'
No comments:
Post a Comment